IDIS
One Solution. One Company.
Premier CCTV Solutions
TOTAL VIDEO SOLUTION PROVIDER
For customers and partners, this means they can build a complete video surveillance and analytics solutions using products that seamlessly integrate from single vendor.

Software Solutions
Enterprise-Class and Multi-Site VMS

HD Analog Cameras
The Most Advanced HD-TVI Solution

Network Cameras
Quadruple Video Streaming for real-Time IP Surveillance

HD Analog Recorders
Overlapped Recording

Network Recorders
Make Your Surveillance Future Proof

Access Control Solutions
Advanced Control for Strengthened Security
IDIS Cybersecurity
PREVENT SUCCESSFUL CYBERATTACKS AND SIMPLIFY OPERATIONS
Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks. Cyberattacks are usually aimed at accessing, changing, or destroying sensitive information.
The IDIS three-part cybersecurity protection system protects your data securely.
Secure Data Access
DirectIP®
Network security through a powerful mutual authentication system
DirectIP® is a proprietary mutual authentication system, supported by all IDIS IP products.
When IDIS IP cameras are connected to an IDIS NVR, both devices mutual authenticate each other automatically through DirectIP. The authentication data is stored and protected on both the IP cameras and the NVR.
Firewalls On NVRs
Firewalls on NVRs utilizing IP and port authentication system
IDIS NVR products have their own firewalls installed that uses IP, MAC address, port and ICMP authentication.
The firewalls on IDIS NVR products are designed and configured to prevent unauthorized access.
Two-Factor Authentication
Multi-factor authentication system utilizing user accounts and registered mobile apps
Two-factor authentication (2FA) is a type of multi-factor authentication system. The user must be certified by the IDIS “Mobile App” in addition to going through the usual login process by typing in a user ID and password.
All IDIS NVRs safely protect user accounts utilizing 2FA.
Secure Data Transmission
TLS (Transport Layer Security )
Data transmission security system combining IDIS’s proprietary technology with TLS
TLS (Transport Layer Security) is a cryptographic protocol designed to provide communications security and data integrity over networks. Integration of TLS into IDIS’s proprietary data security solution minimizes performance impact on video surveillance data transmission.
TLS helps prevent many potential malicious activities, including data snooping, alteration, or destruction of data during transmission over networks.
FEN Security
( For Every Network Security )
Access and data transmission security system over a public network
FEN is access and data transmission security system independently developed by IDIS using P2P technology.
FEN is an automatic network access system. Expert knowledge of routers or NAT devices isn’t needed to set up the system (FEN utilizes Edge TLS for UDP hole punching and port relaying.)
Secure Data Recording
iBank
Protect data using IDIS’s proprietary database system
iBank is a database system, independently developed by IDIS, specifically for video recording. This system maximizes storage efficiency and enables fast data processing.
In addition, storage devices that implement the iBank solution cannot be read by external devices such as PCs, keeping the data safe from forgery and alterations.
iBank is used in all of IDIS’s recording systems.
Chained Fingerprint
Preventing data forgery and maintaining data integrity
Chained Fingerprint extracts distinctive features of recorded video data to use as “Digital Fingerprint” and “Embeds” each fingerprint into the data of the next frame, connecting each frame by frame like a blockchain. Video data created technology can be submitted to courts as evidence.
Chained Fingerprint is a highly efficient technology that verifies the integrity of data, proving it to be authentic.
IDIS Technology
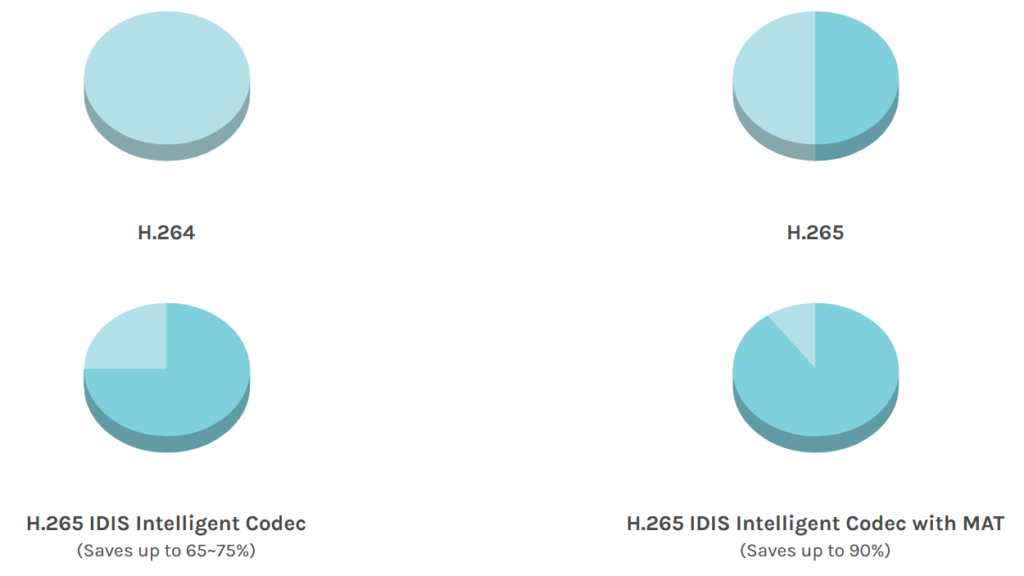
Intelligent Codec
Delivers up to 90% savings on storage and bandwidth, providing faster, better searching of clearer images.
- Lower Your Cost of Ownership : See up to 90% storage savings via IDIS Intelligent Codec with Adaptive Transmission (MAT)
- Search Faster than Ever Before: Faster and soother searches, minimizing distortion while reviewing complex scenes
IDIS Critical Failover
Strengthen fault tolerance with multi-layered protection
If any part of the CCTV infrastructure fails, the system must first recognize the failure and then switch to a redundant system.
This process can take precious time if done manually, and redundant equipment can be expensive.
- Temporary Smart Failover : In Case of an Unstable Network
- Smart Failover: In Case of Network Failure
- Storage Redundancy: In Case of Storage Failure
- NVR Failover: In Case of Recorder Hardware Failure
- Native Dual Power Supply: In Case of Power Supply Failure
IDIS Smart Failover
When the NVR and IP cameras are disconnected, the camera SD card begins temporarily recording.
- Seamless Recording
- 24 Hours Smart Save
IDIS Smart UX Controls
IDIS Smart UX Controls present operators with an advanced and simple to use user interface compared with conventional PTZ controls.
To combat the challenges of IP PTZ controls, IDIS has developed the game changing Smart UX Controls software to provide unparalleled accuracy and ease of use featuring intuitive “Slingshot” and “Rubberband” style controls, creating an experience unlike any other available on the market.